- August 7, 2017
- Posted by: cyberanalyst
- Category: Blog, CEH, CISSP, Consulting, Cyber-security and Ethical Hacking Training

Penetration which is colloquially referred to as pen test is a simulated attack that is being performed on a computer system or its network infrastructure with permissions from management to probe for security vulnerabilities, and a potential means of gaining access to data and other features on the system.
Penetration testing helps one to find out the vulnerability of a system to an attack and if the defense mechanism created are sufficient and which defense mechanisms or techniques employed that can be defeated. A typical penetration testing process focuses on finding vulnerabilities depending on the nature of the approved activity for a given engagement.
A security testing will never prove the absence of security flaws in a system but it can sure prove their presence.
| Want to start an eBusiness and Grow it Globally with free IT, Legal, Internet Discounts,3 Months SME Startup Course, ePayment Integration, Biz Development Services, Free Website, Free SMS Units/Portal all done for you within 30 Days?
Start Here>> Click >>> Start a Digital Business in Nigeria
Brief History of Penetration Testing
In the mid-1960s, for over 50years and more, as the sophistication of networks increased, white hat hackers have been putting in work to make sure computer systems are protected from unauthorized access by hackers. They understood if hackers gain access into their systems, they could even destroy information networks asides stealing information. As computers began to gain the ability to share data or information through and across communication lines, the challenge to protect information increased. These lines if broken and data compromised, contained or stolen.
As early as 1965, computer security experts warned the government and business outlets that because of the increasing capability of computers to share information and exchange vital data across communication lines, there could be an inevitable attempt to penetrate those communication lines during exchange of data. In the year 1967, in the annual joint computer conference which had over 15,000 cyber security experts in attendance, there were serious deliberations that computer communication lines could be penetrated by hackers. They coined the term penetration which has perhaps become a major challenge in computer communication today.
This meeting brought the idea of actually testing systems and networks to ensure that integrity is increased as the expansion of computer networks such RAND corporation which first discovered a major threat to internet communications. The RAND Corporation aliased with the Advance Research Projects Agency (ARPA) located in the US to produce a report known as The Willis Report named after its lead author. The Willis Report discussed this security issue with a proposition of policies to serve as countermeasures in security breaches.
From this report however, the government and organizations started to form teams with the sole responsibility of finding weaknesses and vulnerabilities in the computer networks and measures to protect the systems from unauthorized or unethical hacking or penetration.
Today, there are numerous and specialized options that are available for performing penetration testing. Many of these systems include tools that a range of features for testing the security of the operating system. For example, we have Kali Linux which can be used for performing penetration testing and digital forensics. Also contained in it are 8 standard tools such as burp suite, Nmap, Aircrack-ng, Kismet, Wireshark, the Metasploit framework and John the Ripper. Kali Linux has all these tools and many more and for a system to contain all this sophisticated tools goes to show how much sophisticated today’s technology has gradually become and how many hackers are finding ways to create problems for computer-driven networks and computing environments most the especially the internet.
Objectives of Penetration Testing
The objectives of an intense pen test involve
- Determining how an attacker can find any loopholes to unlawfully gain access to the systems assets that can be of harm to the fundamental security of the systems logs, files.
- Confirming that all the applicable controls like the vulnerability management methodologies and segmentation required for the good functioning of the system are in place
Types of Penetration Testing
- Black box penetration testing: Also referred to as blind testing. Here, the client does not give out any prior information of the system architecture to the pen tester. It may offer little as regards value to the pen tester since the client does not provide any information. It can require more money, more time as well as resources to carryout
- White box penetration testing: Also known as Here, the client provides the pen tester with a comprehensive and complete detail of the network and how is being applied.
- Grey box penetration testing: The client may provide incomplete or partial information of the system network.
Enroll for Certified ETHICAL HACKING TRAINING: Certified Ethical Hacking(CEH ver 9) and Cybersecurity
Click here for Course Modules Details
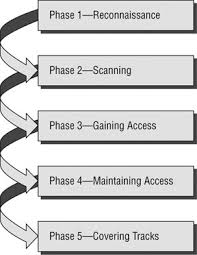
Stages of Penetration Testing
There are basically 5 stages of a penetration test.
1. Reconnaissance and planning: This stage involves gathering intelligence such as network, mail servers and domain names in the bid to understand how the target system works and the potential vulnerabilities it is facing.
It also involves a thorough definition of the scope and the goals of the penetration test, including the systems that are to be addressed and the methods of testing to deployed.
2. Scanning: This stage requires an in-depth understanding of how the target applications will respond to any attempt of intrusion. Scanning can be performed in the following ways:
- Static analysis: This is a process involves a careful inspection of the codes in the application and how it behaves when it is run. These tools have the capability of scanning the entire code in a single pass.
- Dynamic Analysis: It involves a careful inspection of the codes in the application when in the running state. It is a more practical approach to scanning in that it gives the real-time view of the applications performance.
3. Gaining Access: In this stage, the pen tester uses web application attack techniques such as SQLs, XXLs and backdoors to unravel the vulnerabilities on the target system. In a quest to understand the damages they can cause on the target, the tester will try to exploit the vulnerabilities discovered by intercepting traffic, stealing data and escalating privileges etc.
4. Maintaining Access: The stage aims at achieving a persistent presence in the exploited system using the known vulnerabilities. Advanced threats which are capable of remaining on the system for months are logged into the system into to monitor changes, enhancements and any new information being loaded onto the system.
5. Results and Analysis: In this stage, all the results obtained from the penetration test are compiled comprehensively and in details. This includes;
- All the vulnerabilities that have been exploited
- All sensitive data that has been accessed
- The amount of time spent during maintaining access without being detected.
The security personnel then analyses the results in a bid to where necessary reconfigure the organization’s WAF settings and any other application security flaws. This is done to patch all the vulnerabilities and to protect information against any future attacks.
Classification of Penetration Testing
1. External Penetration Testing: An external penetration tests is targeted at the assets owned by an organization that are accessible to and on the internet. Examples of such assets can be,
- The organizations website
- Domain name servers
- Emails
- Web applications
The major goal of the external pen test is to gain access and extract data.
2. Internal Penetration Testing: It attempts to mimic an attacker actually launching an attack on the network to find vulnerabilities or loopholes.
It involves an examination of the IT systems of an internal network for possible traces of vulnerabilities which can affect the confidentiality, integrity and availability, and thereby giving the organisation the clues to take steps to address such vulnerabilities.
====
Enroll for Certified ETHICAL HACKING TRAINING: Certified Ethical Hacking(CEH ver 9) and Cybersecurity
Click here for Course Modules Details====
Penetration Testing Services
I will describe 4 distinct penetration testing service offerings that we can provide you
- Vulnerability Scanning: This scanning technique provides a very transparent and mature offer but the biggest challenge always lies on whether to resell a service offering or to buy that can be used to internally scan the clients systems and networks. Every regulation requires scanning which is the first and easy step taken towards achieving security assurance. This is because all regulated customers need to scan.
- Penetration testing of Infrastructure: This offers tools such as Metasploit or Core Impact, that can be used to perform live exploits. Live ammunitions are used so you have to orchestrate or organize the test with the client in such a way that the amount of disruption during the tests is minimized. The pen tester should endeavor to test all externally visible IP addresses because it is what the bad guys want in order to penetrate the system and network. The tester should also attach to the conference room network which is one of the softest parts of the customers’ defense.
- Penetration of Applications: This is a very important step which involves an attempt to break into the applications because so many attacks are directly targeted at applications. Web applications such as HP’s WebInspect and IBM’s AppScan can be employed, but the tester can also find ways to exploit the application logic errors. Nothing stands a skilled application test because once an initial application is compromised, a direct access to the database where valuable data is easy. If the tester can access the database, then the customers system is owned already and scripts can be written to block every loop holes by the attacker.
- User Testing: This part of the penetration test is always fun for the penetration testers because they get to see how gullible and vulnerable most users are. The test may involve sending fake email messages to customer service representatives in a bid to gather information that can be used to penetrate their facilities. They even drop thumb drives at the parking lot and watch out for people that will plug them. Social engineering is one of the key ways of information gathering and should never be underestimated. Social engineering can be used on the client in order to catch them off guard.
Standards for Penetration Testing Methodologies
There are many accepted industry methodologies that may guide and help the pen tester through any test.
- Open Source Security Testing Methodology Manual (OSSTMM)
- OWASP Testing Guide
- The National Institute of Standards and Technology (NIST)
- Penetration Testing Execution Standard
- Penetration Testing Framework
These frameworks have set standards that any penetration testing activity should follow as should strictly be adhered to guide the pen tester whenever necessary.
A typical penetration activity is detailed and must be carried out in an organized fashion. This is because organisational data and assets are very important and delicate things to handle therefore there is a need to have an orgnised team of professionals to handle your penetration testing services.
We at SOUTECH web consults are the perfect consulting firm for carrying out your penetration testing. We have professional staff and a team to conduct a well detailed and professional penetration testing. Subscribe for our services today.
Enroll for Certified ETHICAL HACKING TRAINING: Certified Ethical Hacking(CEH ver 9) and Cybersecurity
Click here for Course Modules Details
| Want to start an eBusiness and Grow it Globally with free IT, Legal, Internet Discounts,3 Months SME Startup Course, ePayment Integration, Biz Development Services, Free Website, Free SMS Units/Portal all done for you within 30 Days?
Start Here>> Click >>> Start a Digital Business in Nigeria