CEH
-
The Ultimate Guide to Building a Career in Cybersecurity
November 26, 2025 -
How to install Kali Linux in VMware on a Mac computer: Step by step guide
October 2, 2023 -
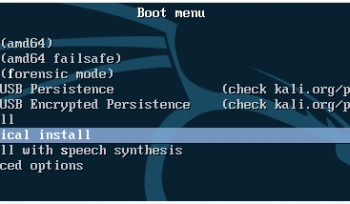
How to install Kali Linux in Oracle VirtualBox on a Windows computer: Step by Step Guide
October 2, 2023 -
How to install Kali Linux in VMware on a Windows computer: Step by Step Guide
October 2, 2023 -
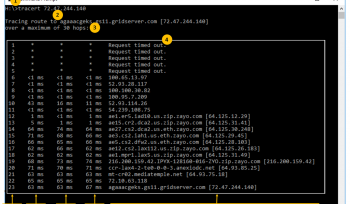
CISCO CyberOps lab – Tracing a Route; cybersecurity training
August 10, 2023 -
CISCO CyberOps lab – Incident Handling ; cybersecurity training
September 1, 2021 -
CISCO CyberOps lab – Convert Data into a Universal Format; cybersecurity training
August 30, 2021 -
CISCO CyberOps lab – Regular Expression Tutorial; cybersecurity training
August 30, 2021 -
CISCO CyberOps lab – Encrypting and Decrypting Data Using OpenSSL; cybersecurity training
August 23, 2021 -
CISCO CyberOps lab – Hashing Things Out; cybersecurity training
August 23, 2021 -
CISCO CyberOps lab – Encrypting and Decrypting Data using a Hacker Tool; cybersecurity training
August 23, 2021 -
CISCO CyberOps lab – Social Engineering; cybersecurity training
August 20, 2021 -
CISCO CyberOps lab – Navigating the Linux Filesystem and Permission Settings; cybersecurity training
August 18, 2021 -
CISCO CyberOps lab – Linux Servers; cybersecurity training
August 15, 2021 -
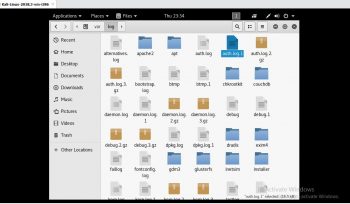
CISCO CyberOps lab – Locating Log Files; cybersecurity training
August 15, 2021 -
CISCO CyberOps lab – Getting Familiar with the Linux Shell; cybersecurity training
August 15, 2021 -
CISCO CyberOps lab – Working with Text Files in the CLI; cybersecurity training
August 12, 2021 -
CISCO CyberOps lab – Using Windows PowerShell; cybersecurity training
August 12, 2021 -
CISCO CyberOps lab – Extract an Executable from a PCAP; cybersecurity training
August 10, 2021 -
CISCO CyberOps lab – Investigating an Attack on a Windows Host; cybersecurity training
August 10, 2021 -
CISCO CyberOps lab – Incident Handling; cybersecurity training
August 8, 2021 -
CISCO CyberOps lab – Reading Server Logs; cybersecurity training
August 7, 2021 -
CISCO CyberOps lab – Attacking a mySQL Database; cybersecurity training
August 5, 2021 -
CISCO CyberOps lab – Exploring DNS Traffic; cybersecurity training
August 5, 2021 -
CISCO CyberOps lab – Class Activity – What’s Going On?; cybersecurity training
August 3, 2021 -
CISCO CyberOps lab – Anatomy of Malware; cybersecurity training
August 3, 2021 -
CISCO CyberOps lab – Using Wireshark to Examine Ethernet Frames; cybersecurity training
August 1, 2021 -
CISCO CyberOps lab – Introduction to Wireshark; cybersecurity training
August 1, 2021 -
CISCO CyberOps lab – Exploring Processes, Threads, Handles, and Windows Registry; cybersecurity training
July 30, 2021 -
CISCO CyberOps lab – Class Activity – Identify Running Processes; cybersecurity training
July 30, 2021 -
CISCO CyberOps lab – Create User Accounts; cybersecurity training
July 26, 2021 -
CISCO CyberOps lab – Windows Task Manager; cybersecurity training
July 26, 2021 -
CISCO CyberOps lab – Becoming a Defender; cybersecurity training
July 23, 2021 -
CISCO CyberOps lab – Visualizing the Black Hats; cybersecurity training
July 21, 2021 -
CISCO CyberOps lab – Learning the Details of Attacks: cybersecurity training
July 21, 2021 -
Google alert
March 3, 2021 -
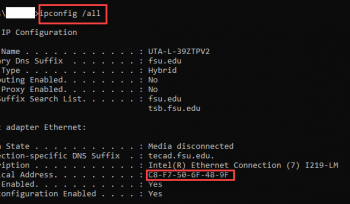
Configuring MAC Address
March 3, 2021 -
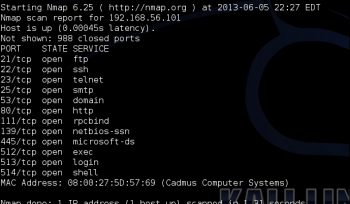
Checking for open port
March 3, 2021 -
Alexa Company Footprinting
February 26, 2021 -
Wayback machine
February 26, 2021 -
Netcraft website information gathering
February 26, 2021 -
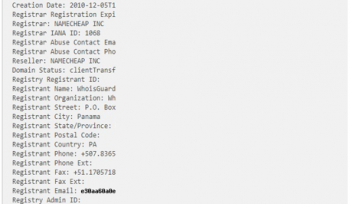
WhoIS Lookup
February 25, 2021 -
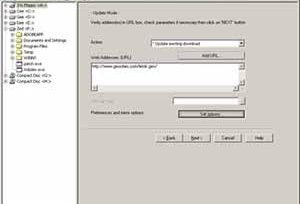
Downloading a Website using Website Copier tool
February 25, 2021 -
Gathering information using Windows Command Line Utilities
February 25, 2021 -
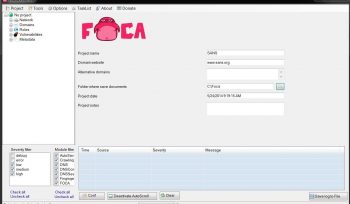
Soutech Cyber Security Lab Test on FOCA
February 25, 2021 -
Soutech Cyber Security Lab Test on Recon-NG
February 25, 2021 -
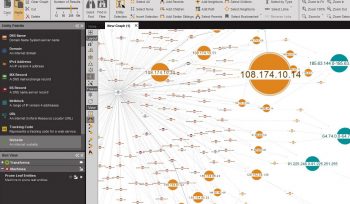
Soutech Cyber Security Lab Test on Maltego
February 25, 2021 -
Infosec Cyber Security and Access Control Training in Nigeria
February 22, 2021
- 1
- 2