- September 7, 2017
- Posted by: cyberanalyst
- Category: Blog, CEH, CISSP, Consulting, Cyber-security and Ethical Hacking Training, Development, Digital Marketing, Mobile Application Development Service and Training, Others, Project and Research Nigeria, Softwares, Technologies
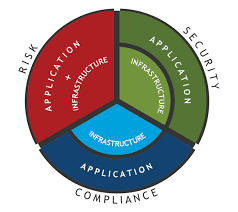
Regardless of whether you are in charge of general IT, IT security, DevOps or administrative compliance, odds are open cloud services are a consistently developing piece of your portfolio. This can be extraordinary for the business, empowering lower costs, more prominent dexterity and speedier speed to advertise. Be that as it may, it can exhibit new and serious difficulties in guaranteeing security and compliance.

The public cloud is a radical new world. In the event that you think customary techniques for securing the data center or firewalling the border will keep your information and applications secured, you might be in for a reality check. The main issue with taking an approach in the form of a legacy approach is that they were not intended for the cloud period, which implies they don’t support or make use of the API-driven infrastructure of the public cloud.
| Want to start an eBusiness and Grow it Globally with free IT, Legal, Internet Discounts,3 Months SME Startup Course, ePayment Integration, Biz Development Services, Free Website, Free SMS Units/Portal all done for you within 30 Days?
Start Here>> Click >>> Start a Digital Business in Nigeria
Whatever your part is in your organization, you can infer huge advantages by grasping a present day, cloud-local model that utilizes equipment that are built on purpose to consistently and consequently screen and oversee security and compliance along the API control plane.
If you are in charge of IT, security or compliance, you can diminish costs, enhance security and affirm more prominent control over cloud technology and shadow IT. In the event that you are in DevOps, you can move rapidly without sitting tight for endorsements from security—while disposing of the potential for the calamity that is continually approaching if appropriate security and consistence balanced governance are not being set up.
Given the proper cloud security platform, the general organization can make of use automation to decrease risk and expel the human components from imperative procedures. Automation enables you to accomplish and achieve a constant visibility scheme over your cloud deployments, empowering reliable duplication among use conditions, for example, improvement, organizing and creation.
Automation, Security, Compliance and the cloud
The adoption of cloud technology moves too rapidly and is liable to excessively quick changes for organizations and firms to depend on manual assets. The major test, be that as it may, is that most organizations still utilize legacy devices, innovations and methodologies to oversee cloud security and compliance.
Luckily, new cloud-local arrangements are presently accessible, conveying an agent-less platform intended particularly for recent modern clouds.
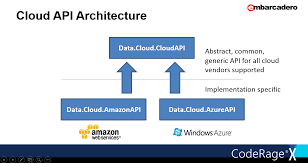
These arrangements use the cloud’s API engineering architecture to determine gigantic adaptability in scaling and overseeing cloud security and compliance.
The steps below therefore will depict how an advanced automated approach to deal with persistent cloud security and compliance works. It depends on the Evident Security Platform from driving cloud security firm Evident.
Step 1
Close Observation: The environment revolving around cloud computing is evolving persistently. These progressions can be ordinary, routine exercises of your DevOps or IT groups; they can likewise be crafted by individuals who might do mischief to your business. As changes are made—over all cloud platforms, services and regions—the cloud security platform screens the designs of the cloud infrastructure to guarantee that it holds fast to security and compliance best practices.
Step 2
Assessment: The security platform safely gathers information about the services in your cloud and constantly performs checks against a progression of foreordained best security standards. It additionally performs checks against any predefined custom marks. These checks decide, on a persistent premise, if there are any conceivably exploitable vulnerabilities.
Step 3
In-depth Analysis: The platform at that point plays out an investigation to decide if the misconfigurations and exposures are prioritized and quantified into high, medium or low risk levels.
Step 4
Automated Remediation: The result of the subsequent analysis being performed is shown on a dashboard and can be sent to incorporated frameworks for auto-remediation work processes to set in.
Step 5
Robust Reporting: Comprehensive and detailed reports are made accessible so your groups can see data involving the risk, as well as client attribution and infected assets.
Step 6
Correction: The groups would then be able to utilize simple-to-follow remediation methodologies to recover the infrastructure to a safe state.
Conclusion
Public cloud is not going to be phased out any time soon but before the decade’s over, people in general cloud administrations/services market will surpass $230 billion, as predicted by Forrester Research. As cloud turns out to be more key to the accomplishment of your organization, it is key that you concentrate on security and compliance, regardless of whether your part is in IT, security, DevOps or corporate administration and compliance.
By grasping a constant security model, your organization will have the capacity to process many procedures that would overpower your groups and frameworks on the premise that they must be done manually. It not just accommodates upgraded security and compliance assurances, it likewise calms the weight on your staff, enhances security for DevOPs and different groups, and brings down the cost and danger of cloud security and compliance.
Cloud computing and its associated technologies is a very broad field. But I have in a few of my writeups been able to discuss the few trends and challenges that is being faced in the cloud environment. To learn more about vulnerability assessments, risk assessments and penetration testing, subscribe to our services at Soutech Ventures to learn CEH course in details.
| Want to start an eBusiness and Grow it Globally with free IT, Legal, Internet Discounts,3 Months SME Startup Course, ePayment Integration, Biz Development Services, Free Website, Free SMS Units/Portal all done for you within 30 Days?
Start Here>> Click >>> Start a Digital Business in Nigeria


