SOUTECH Ventures > Articles by: cyberanalyst
cyberanalyst
-
Google alert
March 3, 2021 -
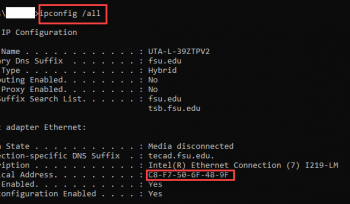
Configuring MAC Address
March 3, 2021 -
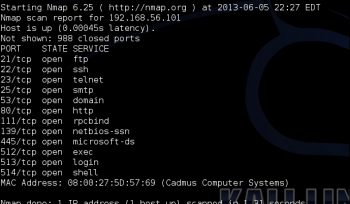
Checking for open port
March 3, 2021 -
Alexa Company Footprinting
February 26, 2021 -
Wayback machine
February 26, 2021 -
Netcraft website information gathering
February 26, 2021 -
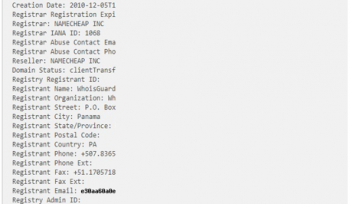
WhoIS Lookup
February 25, 2021 -
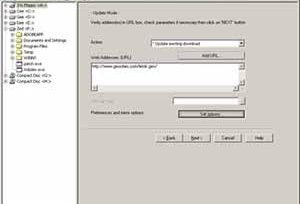
Downloading a Website using Website Copier tool
February 25, 2021 -
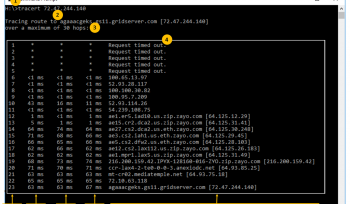
Gathering information using Windows Command Line Utilities
February 25, 2021 -
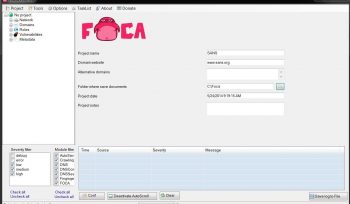
Soutech Cyber Security Lab Test on FOCA
February 25, 2021 -
Soutech Cyber Security Lab Test on Recon-NG
February 25, 2021 -
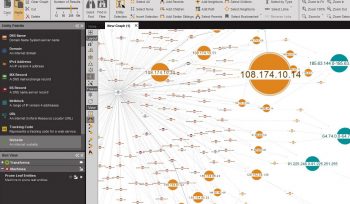
Soutech Cyber Security Lab Test on Maltego
February 25, 2021 -
Infosec Cyber Security and Access Control Training in Nigeria
February 22, 2021 -
Advanced Encryption Package
October 24, 2019 -
Clearing Logs On Windows
October 24, 2019 -
Clearing Logs On Linux
October 24, 2019 -
Hping Commands
October 24, 2019 -
Web Server Security Tool
October 24, 2019 -
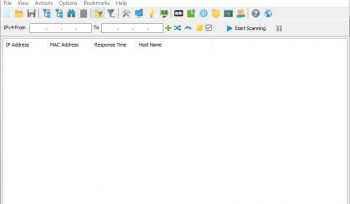
Enumeration Using SoftPerfect Network Scanner Tool
October 16, 2019 -
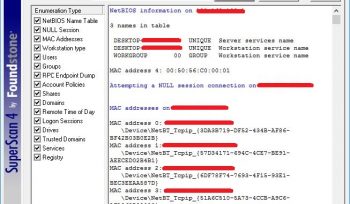
Enumeration Using Super Scan Tool
October 16, 2019 -
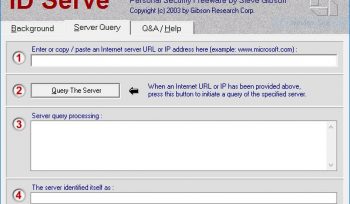
Web Server Foot-printing Using ID Server Tool
October 13, 2019 -
Steganography
October 11, 2019 -
Online Tool For Default Passwords
October 11, 2019 -
Downloading A Website Using A Website Copier Tool
October 5, 2019 -
The Four steps to Bolster cloud security-Cloud Computing-Soutech Nigeria
September 8, 2017 -
Cybersecurity breaches are inevitable; What to do to stay safe- Information Security tips-SOUTECH Nigeria
September 7, 2017 -
The need for an Automated Approach to Cloud Security and Compliance- Challanges in Cloud Computing-Soutech NigeriaEducation
September 7, 2017 -
Six important benefits of IDS/IPS in your business-Secure your network-Tips from SOUTECH Nigeria
September 7, 2017 -
What You Don’t Know Can Hurt You-Cloud Security Issues revealed-SOUTECH Nigeria
September 7, 2017 -
The Secure Socket Layer and how it secures your internet sessions- Be Educated-SOUTECH Nigeria
September 5, 2017 -
BEST PRACTICES FOR PERFORMING AN INFORMATION SECURITY ASSESSMENT-SOUTECHNIGERIA TIPS
September 5, 2017 -
Want to become a Hacker? What you must do!- Soutech Ventures CEH training
August 19, 2017 -
Tutorial on SQL Injection: SOUTECH Ventures
August 19, 2017 -
Terms of Service: Do you ever read them? Stay Informed
August 19, 2017 -
Just how safe are Public Wi-Fi’s?Stay protected- Soutech ventures
August 13, 2017 -
Online Dating: Protect your privacy online-SOUTECH Cyber security Tips
August 12, 2017 -
What is Social Engineering? Protect Yourself and Organization from all forms of Social Engineering-SOUTECH Nigeria
August 12, 2017 -
Setting up a Bring-Your-Own-Device (BYOD) policy for your Organization- Be Cyber-safe-SOUTECH
August 12, 2017 -
Protect your Infrastructure-Know the Importance of Firewalls : SOUTECH Cyber security training program Nigeria, Africa
August 7, 2017 -
Understanding the importance of an IT audit: SOUTECH Ethical hacking tips
August 7, 2017 -
Has your account just been hacked? Wondering what to do next?
August 7, 2017 -
All you need to know about Polymorphic Viruses
August 7, 2017 -
Network Penetration Testing Services: Tools and Methodologies
August 7, 2017 -
Vulnerability Testing: A Detailed Guide-SOUTECH guide
August 7, 2017 -
What are Man-In-The-Middle Attacks: SOUTECH Ventures cybersecurity training in Nigeria, Africa
August 7, 2017 -
All you need to know about Penetration Testing: Soutech Ventures
August 7, 2017 -
Performing a Detailed Penetration Testing: Soutech Ventures
August 7, 2017 -
Why do you need a Vulnerability Test? Concepts and Methodologies
August 7, 2017
- 1
- 2