Digital Marketing
-
The Future of Digital Marketing: Emerging Trends and Innovations
September 13, 2023 -
The Future of Content Marketing: Emerging Trends
September 12, 2023 -
Social Media Crisis Management: A Guide for Digital Marketers
September 12, 2023 -
Email Marketing Best Practices for Digital Marketers
September 12, 2023 -
Social Media Advertising Strategies for Digital Marketers
September 11, 2023 -
Content Marketing Strategy: Building a Strong Foundation for Digital Success
September 11, 2023 -
Influencer Marketing Strategies for Digital Success
September 10, 2023 -
The Power of Storytelling in Content Marketing
September 10, 2023 -
Crafting Compelling Social Media Content: A Digital Marketer’s Guide
September 10, 2023 -
Step by step guide on product design part 1
August 13, 2023 -
5 ways to improve your SEO
January 19, 2021 -
Massive Discount on all our Trainings
January 11, 2021 -
Creating a brand strategy for individuals, small business and enterprise. Step by step guide
October 2, 2020 -
Google Maps to Add New Feature That Shows Places With Highest COVID-19 Outbreaks and Infection Rates
September 8, 2020 -
Biz Plans, Feasibility Report, Grants & Proposal Writing
August 26, 2020 -
Why content is the king?
August 25, 2020 -
Pro Digital Marketing and CRM
August 21, 2020 -
Human Resource Management
August 20, 2020 -
Graphics, Branding, UI/UX Design Professional
August 18, 2020 -
MEGA REWARD FOR SOUTECH FACEBOOK TOP FANS!
August 9, 2020 -
Integrating Blogging into a Business Strategy
July 20, 2020 -
WordPress Subdomain | How To Install WordPress On Subdomain? SOUTECH Hosting
October 19, 2019 -
October 2019 Professional IT Training: website design, ethical hacking, digital marketing, data science abuja
October 10, 2019 -
SOUTECH Hub Free Digital Skills Training
October 1, 2019 -
Choosing a Blogging Platform for your Personal or Business Blog
September 26, 2019 -
Professional IT Training in Owerri with Amazing Bonuses: Data science/Machine learning, Digital Marketing/Growth Hacking, Cyber Security/Ethical Hacking, Solar and Inverter
September 21, 2019 -
Creative ways to promote your business on facebook
August 16, 2019 -
Building your website with WordPress – Differences Between www. wordpress.org and www.wordpress.com
August 16, 2019 -
Mata Tags and Meta Keywords – What they are and how to use them for website indexing
August 16, 2019 -
Technical SEO – The best Practice on How To use it to Rank Online
August 16, 2019 -
SME Business Development – 10 Marketing Business Strategies SME businesses Should Explore
July 19, 2019 -
Social Media Marketing (SMM): The Marketing Essential for Your Business Growth Online
June 28, 2019 -
Career Tips: Ways To Earn Money As A Front-End Developer
June 6, 2019 -
digitalowerri
May 16, 2019 -
Best Content Marketing strategies: A smart guide to setting your own content strategy Part 2
May 3, 2019 -
Best Content Marketing strategies: A smart guide to setting your own content strategy Part 1
May 3, 2019 -
How to Create Clipping Mask in Photoshop
May 2, 2019 -
Valuable Basic SEO tips to get you started as a digital marketing newbie in 2019
May 2, 2019 -
Simple Guide through Photoshop Tools and Options
April 26, 2019 -
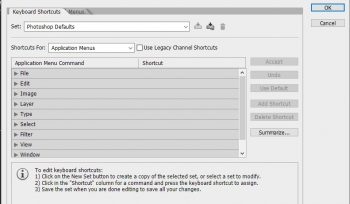
Setting Up Your Custom Keyboard Shortcut On Photoshop
April 26, 2019 -
Proper Color Usage in Graphics and Branding
April 23, 2019 -
FONT PSYCHOLOGY: USAGE AND RULES
April 3, 2019 -
HOW TO RECORD YOUR PHOTOSHOP ACTIONS
March 28, 2019 -
THE MOST SIMPLEST WAY TO USE THE PEN TOOL IN PHOTOSHOP
March 28, 2019 -
EPIC WAYS TO USE PHOTOSHOP- The Use of the Selection Tool.
March 27, 2019 -
Navigating your business: a breakdown of a basic business model canvas
February 11, 2019 -
Guidelines on how to write a simple business profile
February 11, 2019 -
How to Project Manage Your Web Development Application from Start to Finish
February 8, 2019